Recent high profile breaches underscore the fact that data loss prevention (DLP) technologies are not as effective as we would hope. These data loss prevention technologies often fail to meet an organization’s list of data protection requirements, because there are so many vectors for the exfiltration of sensitive data. A complimentary solution to aid in the detection of data breaches and the exfiltration of sensitive information is the InQuest Deep File Inspection DFI technology. Deep File Inspection, or DFI, is the reassembly of packets captured off of the wire into application-level content that is then reconstructed, unraveled, and dissected (decompressed, decoded, decrypted, deobfuscated) in an automated fashion. Exposing these embedded content enables heuristic analysis to determine the intent by analysis of the file contents (containers, objects, etc.) as well as the semantic content as an artifact. Deep File Inspection as a technique is higher level than Deep Packet Inspection, where individual packets or connections are judged to be benign or malicious, but faster than sandbox approaches that attempt to classify a sample by its effect on a system. This speed advantage allows DFI to be deployed in computing environments where carrier-class network volume demands quick triage of traffic. A file can be evaluated as benign, suspicious, malicious, or sensitive in less than a second rather than minutes In the context of Data Loss Detection, File Artifacts containing sensitive information will be un-earthed. At the lowest level, intellectual property, payment data, personally identifiable information, and even institutional classification marking can be easily identified by leveraging the included or User-Defined signatures. 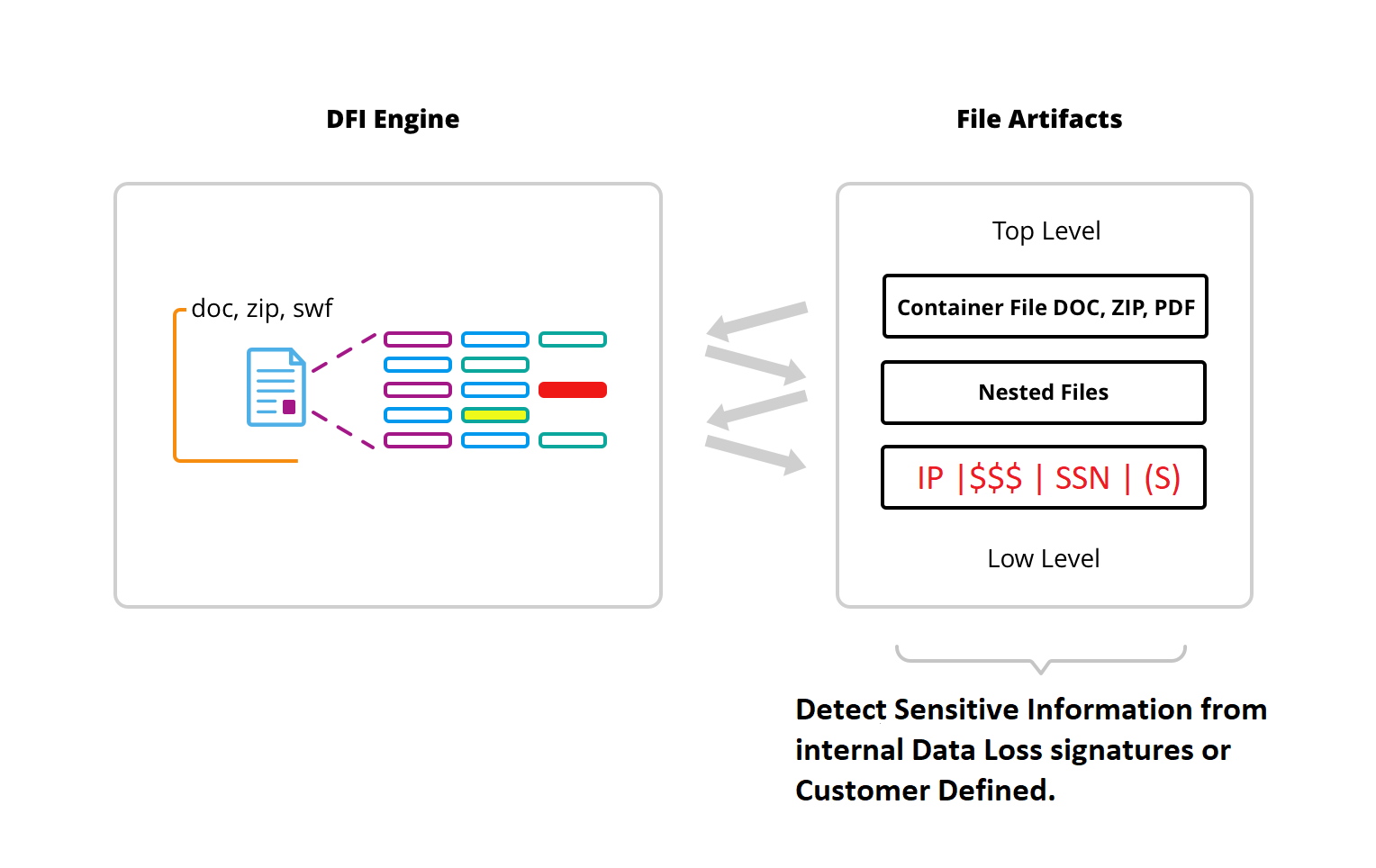
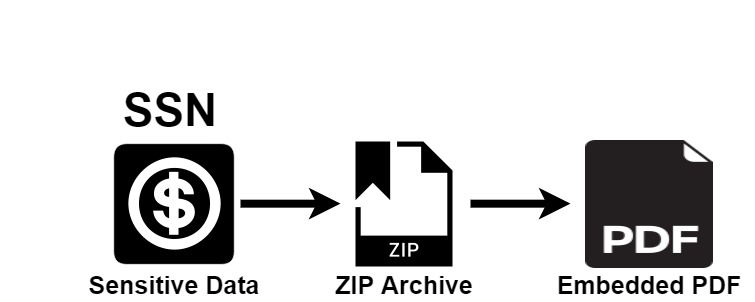
The DFI process is able to identify sensitive information within embedded files with high fidelity. In the following example, SSNs are listed within a spreadsheet. The spreadsheet is then archived and embedded within a PDF. The DFI process unnests the embedded file and identifies the existence of sensitive data.
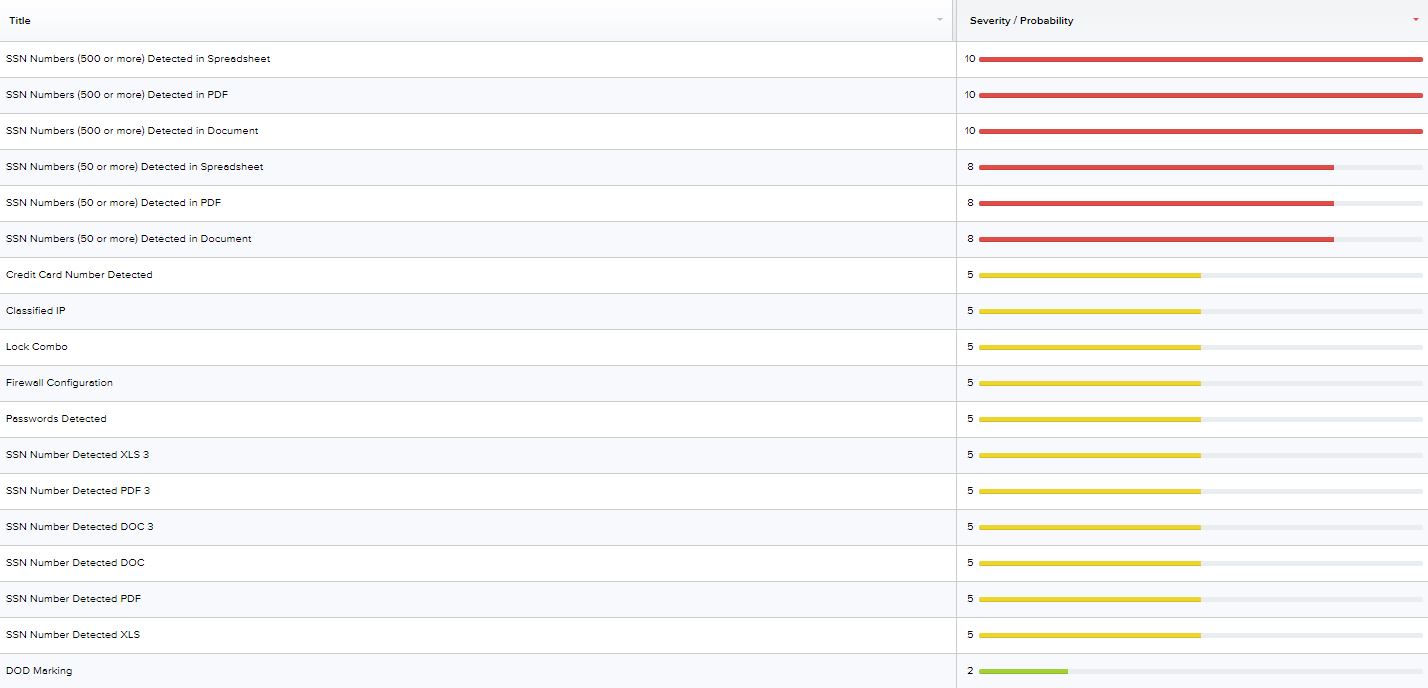
Data Loss is one of the signature categories available within the InQuest Platform. The combination of events can be used to quickly triage a file or session event. The culmination of multiple signatures is used to dynamically adjust the Exposure or Threat Score. 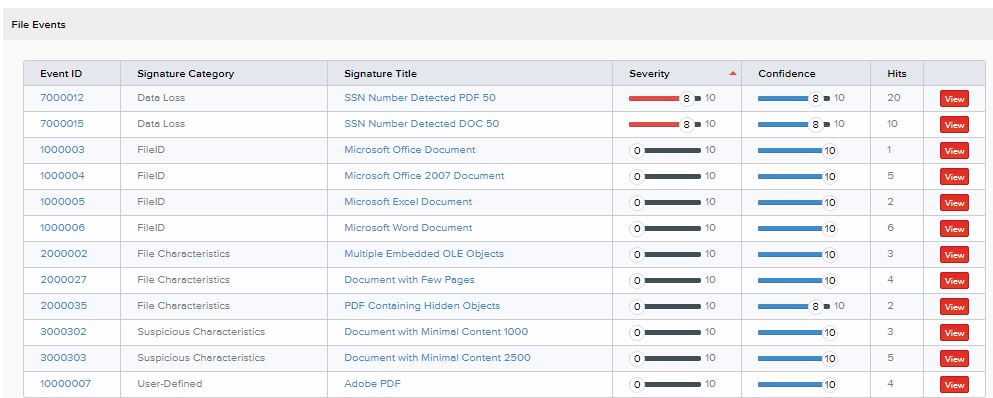
The ability to view signature hits in-line within the analysis page provides the opportunity to quickly confirm the existence of sensitive information. Pre-defined signatures are also able to detect user credentials, passwords, lock combinations, or anything specific to your organization with a User-Defined signature. The ability to analyze Data-at-Rest provides the opportunity to find sensitive information on network shares or other critical assets. The perfect complement to retrospective file analysis, Data at Rest Deep File Inspection (DFI) provides a sentry at your endpoints and critical storage locations. Scan potential threats that were introduced via peripheral media or encrypted protocols. The currently supported SMB versions are SMB1, SMB2, SMB3, and SMB3.1.1. 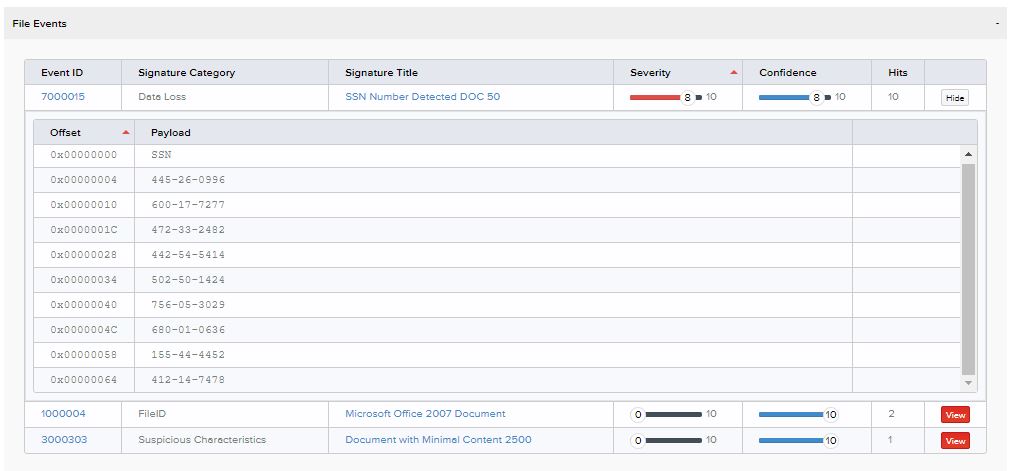
Another differentiator InQuest provides for detecting data-loss is Optical Character Recognition (OCR). One example of leveraging OCR for detection capability would be scanned documents that contain PII. OCR is is a necessary technology that can be used to identify text within images. whether these images contain sensitive data or are of the coercing the user to enable macros. InQuest provides your organization with additional visibility into Data-in-Motion as well as Data-at-Rest. Whether you are dealing with Personally Identifiable Information (PII), Protected Health Information (PHI), Payment Card Information (PCI) or helping to secure important intellectual property or state secrets, InQuest’s Deep File Inspection will provide improved scrutinization of session and file events.