Cyber Security News | Notorious Mystic Stealer Attacks 40 Web Browsers & 70 Extensions to Steal Login Credentials
Originally posted on Cyber Security News here
Written by Guru
A brand-new information stealer named Mystic Stealer appeared in April 2023; nearly 40 web browsers and more than 70 browser extensions had their credentials stolen by Mystic.
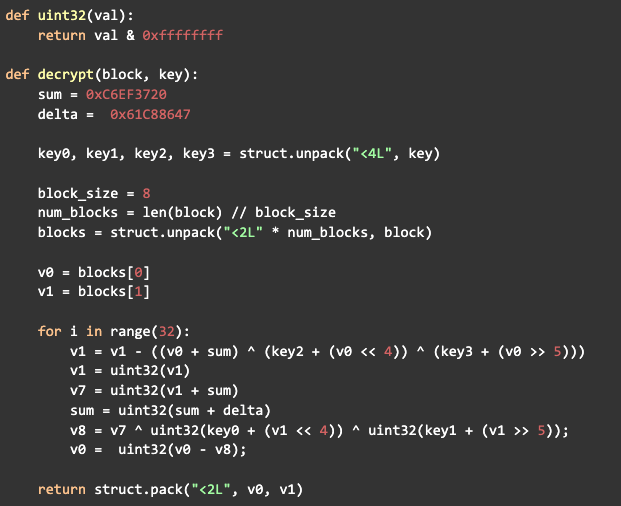
This spyware also targets Steam, Telegram, and cryptocurrency wallets. Additionally, the RC4-encrypted proprietary binary protocol is implemented by Mystic.
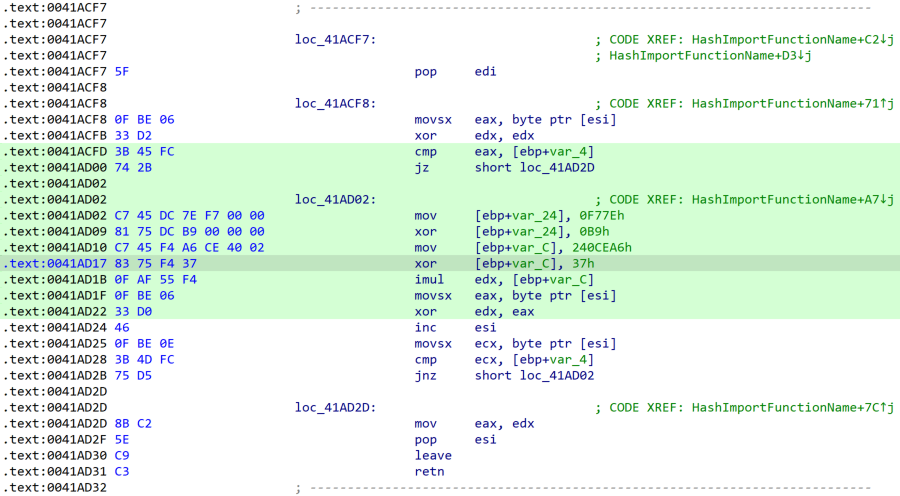
Particularly, the code is substantially obscured using polymorphic string obfuscation, hash-based import resolution, and runtime constant computation.
Working of Mystic Stealer
Together, Zscaler and InQuest offered an in-depth technical analysis of the malware. Mystic Stealer specializes in data theft and can steal a variety of different types of data.
It is intended to gather computer data such as the system hostname, user name, and GUID.
Additionally, it determines the geolocation of a likely system user using the locale and keyboard layout. Key Data may be extracted from cryptocurrency wallets and web browsers using Mystic Stealer’s functionalities.
It gathers information on cryptocurrency wallets, browser history, arbitrary files, cookies, and auto-fill data.
Mystic Stealer is equipped to handle any major cryptocurrency wallet, including Bitcoin, DashCore, Exodus, and more. Mystic may also steal Steam and Telegram login information.
To decrypt or decode target credentials, the stealer does not require the integration of third-party libraries.
“Mystic Stealer collects and exfiltrates information from an infected system and then sends the data to the command & control (C2) server that handles parsing”, researchers said.
List Of System Data Gathered By The Malware
- Keyboard layout
- Locale
- CPU information
- Number of CPU processors
- Screen dimensions
- Computer name
- Username
- Running processes
- System architecture
- Operating system version
The cyber security news learned that the malware targets over 70 web browser extensions for cryptocurrency theft and employs the same capabilities to target two-factor authentication (2FA) services.
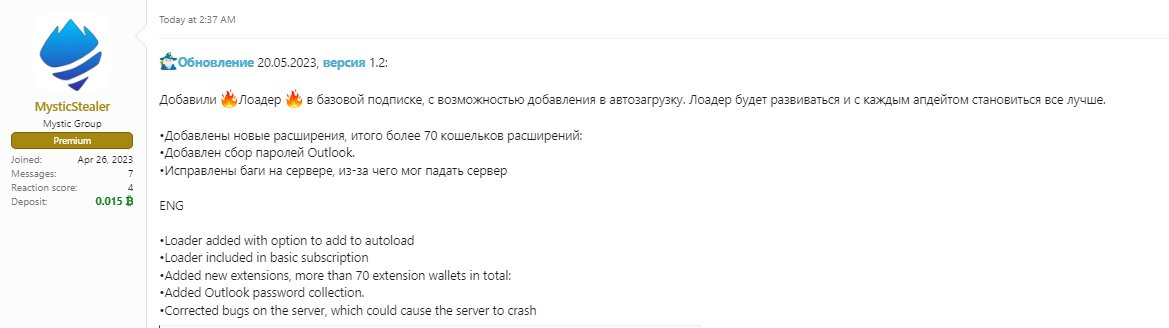
The capacity to download and execute new malware payloads is referred to as a loader.
This reflects a continuing trend in which loaders enable one threat actor to promote the dissemination of affiliate malware on compromised devices.
Further, the constant values in the code are obfuscated and computed dynamically at runtime.
Mystic Stealer uses a unique binary protocol over TCP to interact with its command and control (C2) servers.
The stealer has been associated with many server-hosting IP addresses in a wide range of countries, including but not limited to registrations in France, Germany, Russia, the United States, and China.
Additionally, researchers mention that some servers are found in the hosting areas of Latvia, Bulgaria, and Russia.
Since Mystic Stealer is a new player, it is challenging to forecast its future. But it’s a sophisticated danger with the ability to cause significant harm.