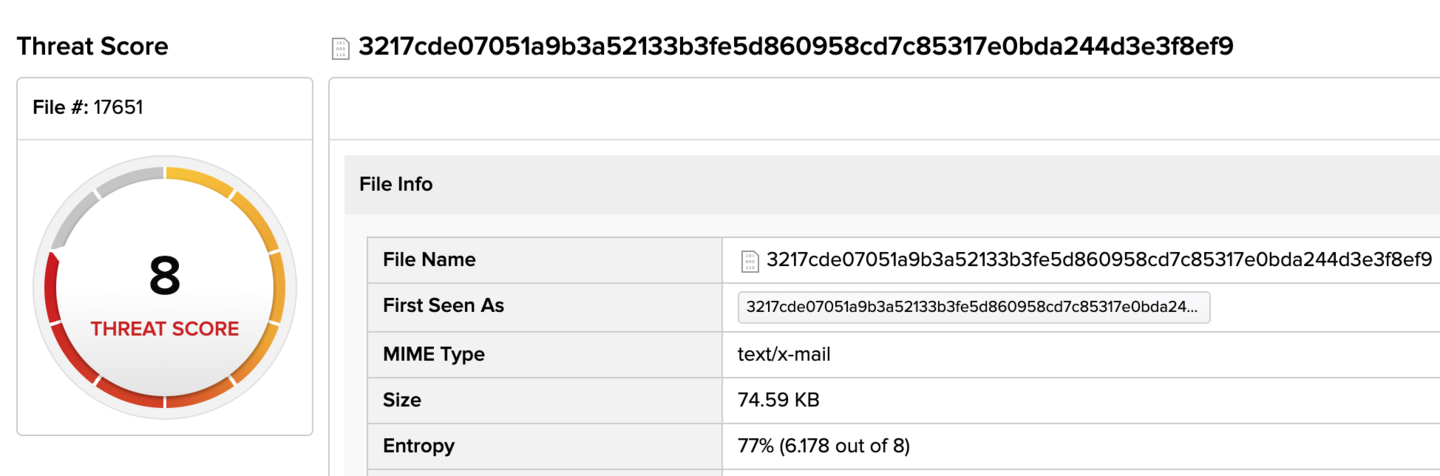
In this quick, end of the week post, we wanted to touch on the ubiquitous COVID-19 (aka Corona Virus). Sharing an interesting lure, related malware, and some IOCs for colleagues to dig into while society on a whole is relegated to solitude in our homes. Our posting here is in no way comprehensive. There is a myriad of malware campaigns, disinformation operations, and general scamming revolving around the very concerning topic. Our goal is to further awareness and share some knowledge in the process. Whenever big events are happening, scammers of all stripes rise up to take advantage of people’s concerns. Email-based scams will often use keywords taken straight from the headlines to capitalize on people’s (very legitimate) concerns. Side note… automating the creation of semantic hunting rules from a news feed is of value. The COVID-19 threat landscape has gotten out of hand with an astronomical amount of nefarious activity. The interesting part is that these types of emails will inevitably be sent out to a wide range of recipients while somehow bypassing security checks. Users then fall prey to these lures that reference relevant topics and interests pertaining to current events. This one happens to be about products “available for purchase” relating to the influx of demand as a result of COVID-19. Depicted below is the InQuest threat score (8/10) for a lure delivered via e-mail with relatively low AV detection, 5/59 on (VirusTotal)
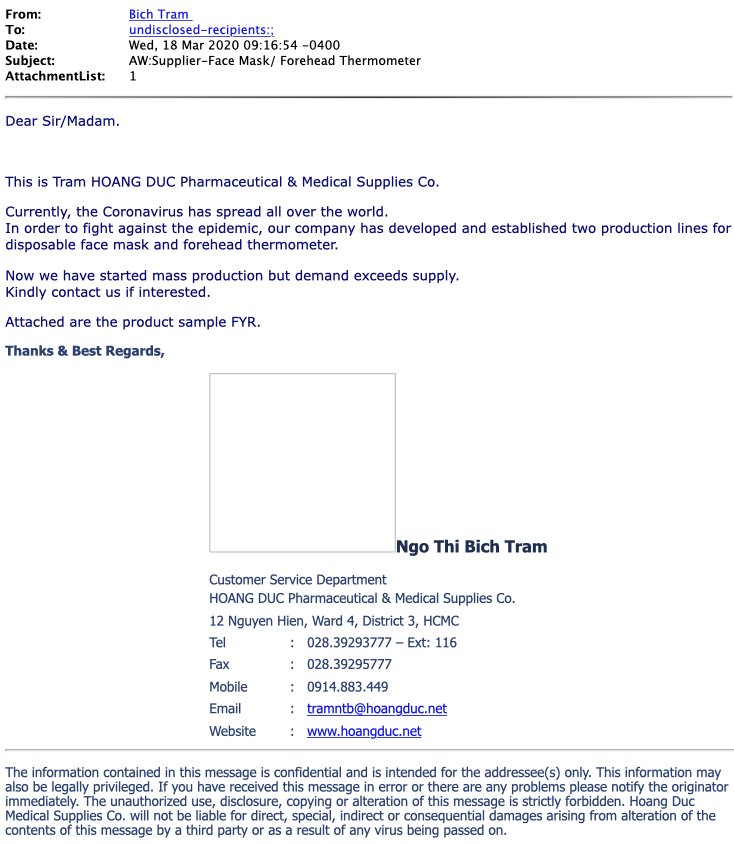
The Email Lure
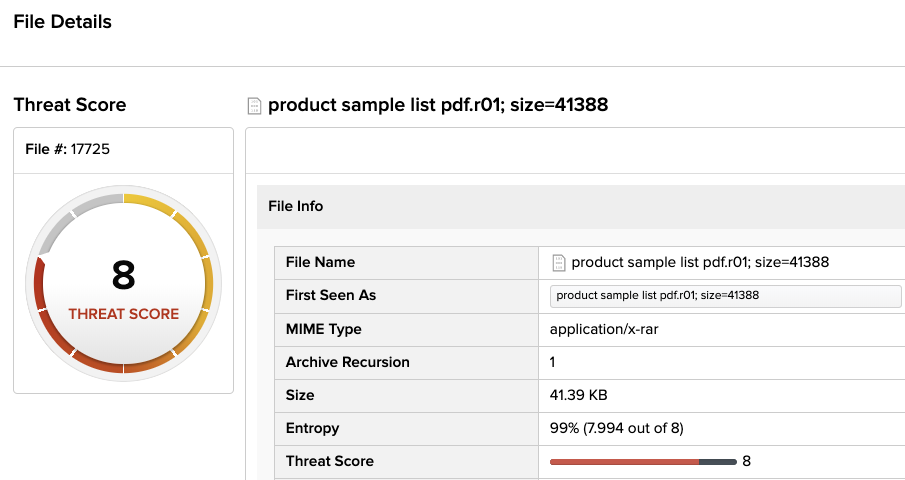
The .RAR file also has relatively low detection rates with AV, only 7/61 vendors on (VirusTotal) detected this sample.
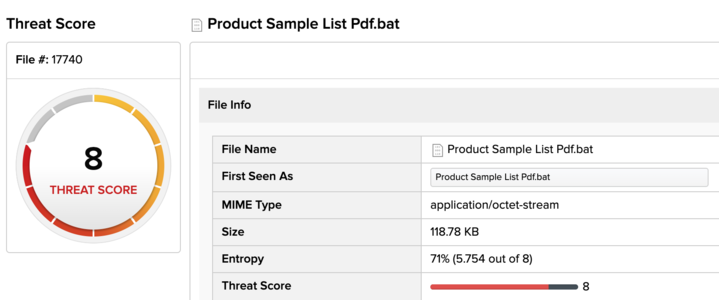
This is the .BAT (batch) script file that was inside the .RAR archive, there is decent AV coverage for this batch script as 27 of 72 vendors on (VirusTotal) detect the sample.
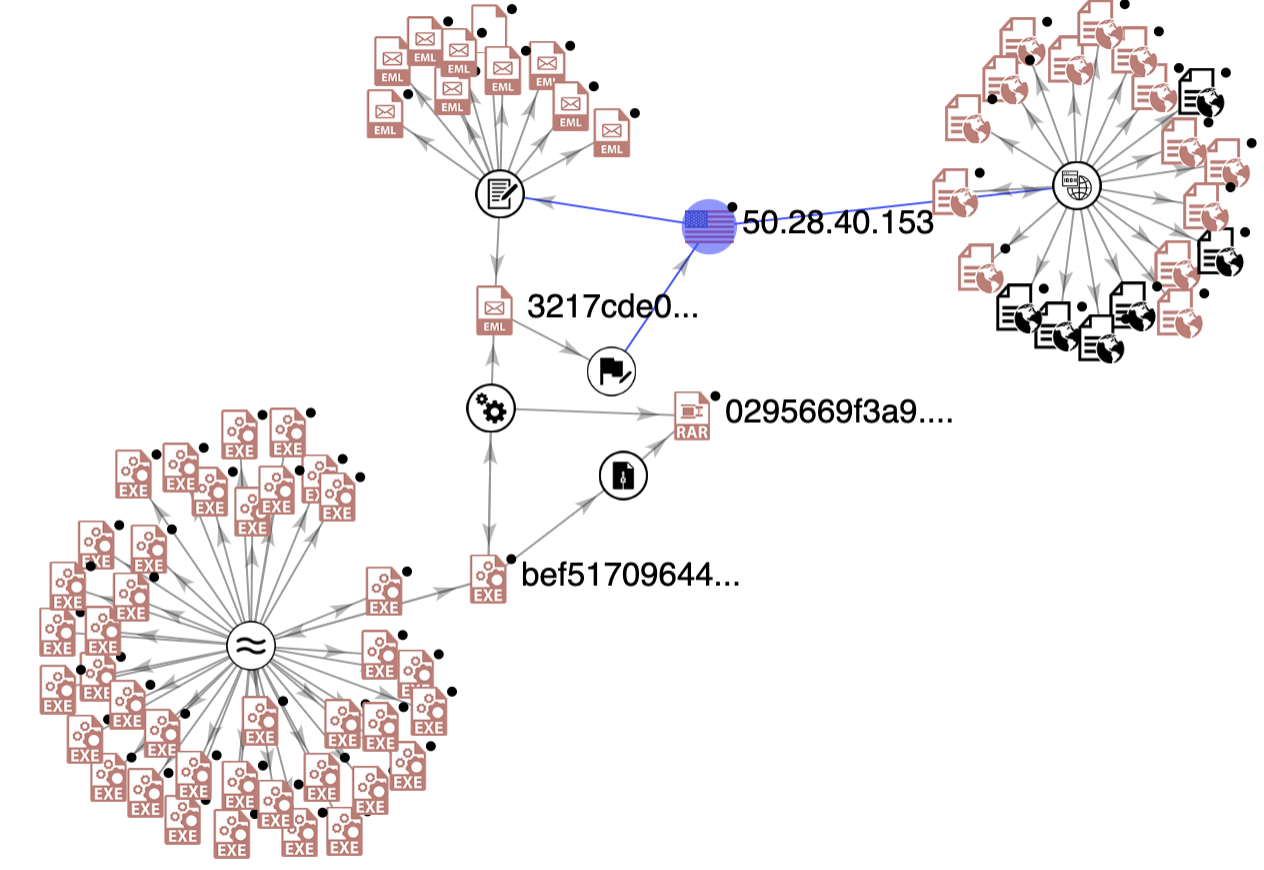
Loading some of the IOCs above in VirusTotal’s graph tool allows us to draw links between similar files and expand our pool of known indicators that are leveraged by this campaign. We observed GuLoader to be one of these payloads, based on our review of an encrypted blob we extracted.
We’re still actively digging into an evergrowing pool of samples and campaigns. For researchers that lack access to commercial tooling like VirusTotal we invite you to tinker with and give us feedback on InQuest Labs. In line with the content of this post, explore a stream of Microsoft Office documentations in search of potentially malicious document lures referencing “(COVID)”:
- https://labs.inquest.net/dfi/search/ext/ext_context/covid
IOCS from Threat Sequence
- 3217cde07051a9b3a52133b3fe5d860958cd7c85317e0bda244d3e3f8ef98de7
- 0295669f3a9566bd16e93cffaef73f97df74996be49a35237d1f254980414eb9
- bef51709644abbeadd8d9bfdc9b4430b857250b7319cc6c5f235c0accc72dc01
- https[:]//drive.google[.]com/uc?export=download&id=19ZjXFuaXbuo4TC7eOMiubChN4C9Nb8wm
- ba5f06cc293b94d8f74b65411363c7384645c84a5304e8824fe93e7e675f7cee
- 50.28.40[.]153 AS32244 | US | LIQUIDWEB
Hashes for the Curious to Explore
- bef51709644abbeadd8d9bfdc9b4430b857250b7319cc6c5f235c0accc72dc01
- 0295669f3a9566bd16e93cffaef73f97df74996be49a35237d1f254980414eb9
- 3217cde07051a9b3a52133b3fe5d860958cd7c85317e0bda244d3e3f8ef98de7
- d6c051175eb1ed27c293e74b875c92a92641b6e46838ccabf8042a0045ae9d73
- f4a485cd4df7994264aa6c334331d56f8d9e620a9aa05fe5895cd5e69ea957cc
- 17ae283aefe04719ab7bc2591d9aff9ffc5c9ebbde2de497248f3f20b9e0d3c0
- 9cf4c124abf7597ea50782da208dfe821b1549884a26ae6d49a4218e203bf6fa
- 6583bc4be54b1daa0b61ae646dc2373146e0f9e16dc8fdaccedf4bf40ac18e22
- 5c86fcf32d1f15a745dd2f39989630ac310d1aee52af7b5f762f75f8855879ab
- c2800d1789bfdc0191c2c7f3d5051033dabc4a27fe965360e18926b36701a812
- 0fb6ddb43fd28560878fdbfcb697197d3d55e41d10bd284d4e5a669568b85594
- 6193b91fbab7d782abd2cd0d5c62825a90a51a636377a4abe6f80a323173c0f1
- 71896ec3c8b53386d7a40c8b2f4a2cc7fefd2244cd9dd3ea389c188ef5836d66
- d9d9510653e5ea44db0d23dea2928fbde983d0d89225095eacc123df20c1b257
- 7388152e3413d63be30499fe2e2e46467a53838e70e584c15d89619ccffb5731
- 0fc9df882190bf37ec0f41d27044c958718cc3ca66b830f88f915a2ff53d3ba5
- 1876fa5288dc34e67930a71b105ad347b6e45d90ee359c3288462ace16c7ec12
- 2ab09792b39bea342095fba95aa903946ea28d4489c3b92fde0db86da4973b05
- e5840a4cc91cad08ca0b1b24ed1664c44df75baaabd5aa9aafc9a6bd8793d6ae
- 719091f95f9b383d3e228ea26703f67d942a6d6a1094491dc2aa0ea1295feaeb
- db740f36a91f4fa311184714bdb059022ba29a054975db509a5bb782eb542533
- d462b8019253e22180fc26e89fd665de78a567501981f6c7149096669a860b97
- 7a0b40e7e0d45682fe36fd5008ff5e56457c5348cc576b83ba66426784d701e7
- 65cabdb117f954f4518a753c8e57eaededa0218904afee600fab7b92efbaca7b
- 40c3bedafbab078656c8f4db68eeed72b02d093cb0e278c7d947c2a9636e356c
- e6cded7d3c16dbe565de42308089d13b098fbf2abbb6df3abc5cfe35f01fd380
- ce9294deb0ccbe0b09e456b4e493484090f8c6df8d121f39cd272372886c3e0d
- dd75db97eb324e75f9b8a5b22dbdf763969e5672e484c75d95a2b0e7c21192ab
- 2980f8dd124fdb074759b104571cbef45b9fa74a14ec37b898026943c511b5a2
- f4608c618089f98a4c9f3a4d15f5fdf93c3bd2e6a8f4992e4c4a261cadd8210c
- 6c899c4f40b60c98d218a854edf617e5d46b2e7064b9760c5dfe9745ed91eded
- 170bdb74ebbffb2a2cf0da341dac0f29e9dfff66a5380349cef64a78edd622e3
- 4f7d754cdeba887a5eccb0eda6a787dc0ac30f50b701b180ee1f9b738ef1daf1
- 9eb92a149da1764db7347db4261bcd018cb7110ecfd8c94276a25f48e6ca2594
- c16c8dd5538b1120eeefceab7928d93d0b409ede8cbc6625aaf2ea5657544627
- 3b9d9aaef7455f49766572c662ff8be7de575d668c382cb70ff2e83537b7b6f0
- 1a1b9fa9bba2a681f34d48e420da174b0fad6ab881268c05fcb1867bafef7199
- 3a0cde58b3274527d1a140011aeb37e97d6b5e90a11bb5d99757de06fab5d83f
- d2cd734c7d08fe8a5f1f65e319a3204f0c8b46ea224f1b90b3c8a6d0c6de586a
- fc880cc68a2d311c9ebb3d3f29114855b14d41d6d06b91195131d18455b95df9
- 1ad06524edd2028683784c294a1a7b6f93c76018ae0e07efec8b10e002de331d
- 6b0e95a0381d6b121aeaf0cb65901f61d97267bb190f6b972e295862a24bc2ec
- 9ad3b6cb49110096fe95dfd2619ec6eeacbe3fd18fd4e94079691544f794bddd
- 92b3b4f390b889a2d6a6a6ed80daf8f58e6c37722feb13f227d0f7dc92e151f1
- 5524206533f42b0af70cb550cc2ba8e2b46809666871777f7370ee9d43b8b87a
- 71a47c1f83c4206102335047cd2f897c98e7a2d2bb975c124fdfe8ab3d0d0560
- bb5df684c0be43031bf07fb7a6e435fcf956b85f3344e9b0e7d51aa6cd6ec717
- 543cc8e5d2c11b35a36199aa10af3399ad847fd1f81b8de99903eb1ef1cb1f33
- ca08afb0c85a02e390e8f28f5242f4da2e1dfa8f0eed6319042fb589ac04973d
- 0c7a8616bbef5c063705ca82e9331428e5b1c7e11808ffe1913162ba4268c9ba
- f35b160cae2f87ce82183946da28bd88891b0e46f95353fe68efcc2d2a59e244
- 11277d01a3c3a1d8af9f41ffde1efe2843f6232266a68a05bfe65e21d8348ea2

