Due to the variability in anti-virus and malware detection methodologies, organizations can benefit from the coverage that a multi-AV solution provides. To facilitate this, InQuest includes OPSWAT MetaDefender as part of its network-based malware detection products.
Overview
The last few years have seen a wider than ever set of possibilities become part of the modern threat landscape. Trojaned binaries via update hijacking, supply-chain interdiction, watering hole attacks, and “fileless” malware delivered via spear phishing (will provide links to incidents). A single antivirus or endpoint protection product limited by the its techniques and technologies, but OPSWAT Metadefender reduces your network’s malware blind spots with the benefits of its multi-scanning. The face of advanced malware threats today requires this multiple engine approach, which is why InQuest incorporates Metadefender Core as part of its network-based malware detection solution.
What Metadefender Can Do for You
With over thirty embedded anti-malware engines, OPSWAT provides customers with high-security networks the peace of mind that the complexity and volume of today’s malware is matched with the protection of a defense-in-depth multi-engine scanning solution. Combining signatures and heuristics from these engines allows the system to process files at high speeds, and equips your analytical teams with the benefit of signatures supplied by malware researchers from around the world, each seeing a different subset of malware samples.
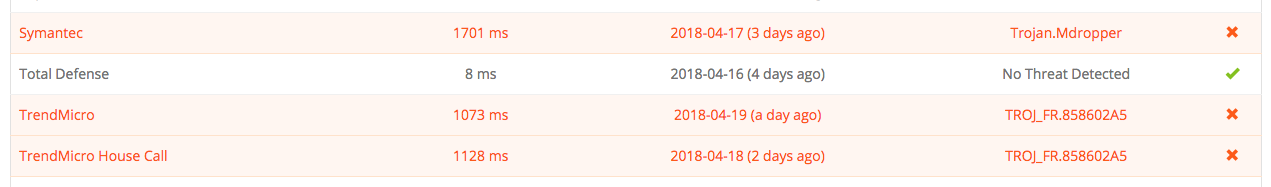
As an example, here’s an example where a ZIP-compressed malware sample is present in some of the AV signature sets, but not others. As of this writing, the file is detected by 25 AVs, but this illustrates the disparity that can occur between AV results early on in a malware campaign:
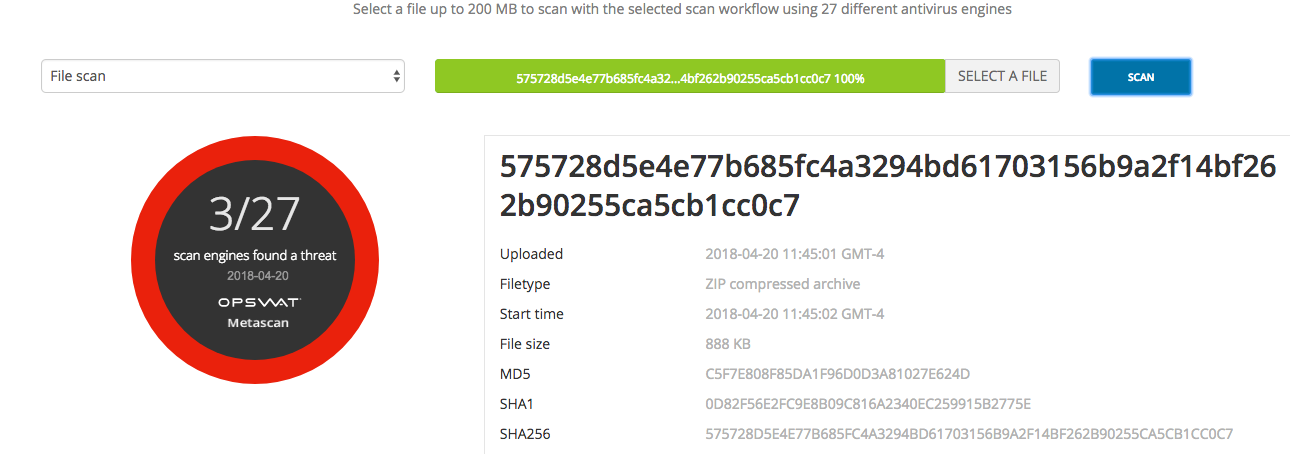
Malware can have wildly different detection rates based on AV engine features.
Supporting deployments in on-premises and air-gapped environments, as well as a cloud-connected mode, Metadefender can also operate as an active integration of InQuest in a wide variety of deployment scenarios. Augmenting this is OPSWAT’s rich set of APIs, assisting users in integrating into their network architecture, visualization framework, and reporting mechanisms.
On-Premises MultiAV for InQuest’s Flexible Deployments
While some environments support retrieving anti-virus and threat results from the cloud or anti-virus vendors directly, many customers require a local, on-premises solution. The reason may be a segregated or air-gapped network, or simply the privacy and operational security (OPSEC) afforded by keeping all malware analysis local. Recent reports concerning AV vendor exfiltration and handling of files, along with the need in some situations to keep knowledge of malware threats close for counterintelligence reasons necessitate a multiAV solution that works right beside InQuest in these local environments. Retrieving results from VirusTotal for files can present a loss of privacy for sensitive files at best, or an unacceptable operational risk at worst. OPSWAT Metadefender solves this by allowing secure multiAV scanning to be done locally.
InQuest allows customers to capture and detect from all data passing in-transit on their network. Endpoint based solutions can present additional overhead or attack surface, and may not capture the full scope of a malware campaign attempting to enter a network. Simple gateway AV, on the other hand, often lacks the picture to accurately characterize whether or not a given session is malicious in nature. By running on network traffic in-transit, and doing deep file inspection, we can analyze sessions based on file intents, before any execution or exploitation can take place. Augmenting this by bringing the capabilities of multiAV to bear on the full volume of network traffic without having to sacrifice privacy is an enormous benefit to an organization’s security posture.
Factoring MultiAV into Threat Scoring
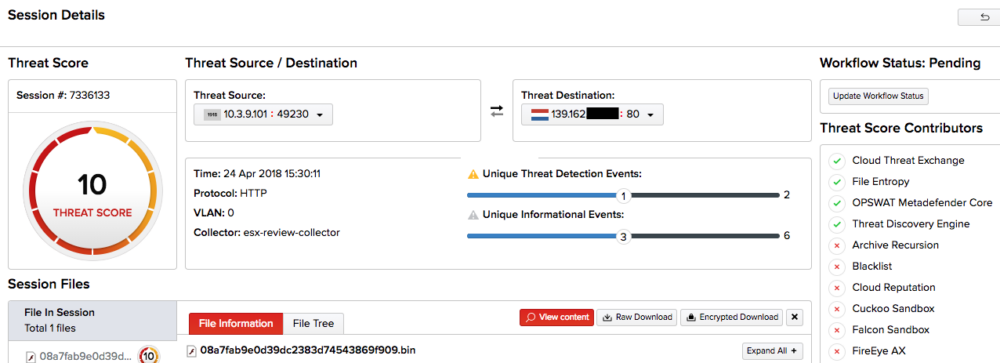
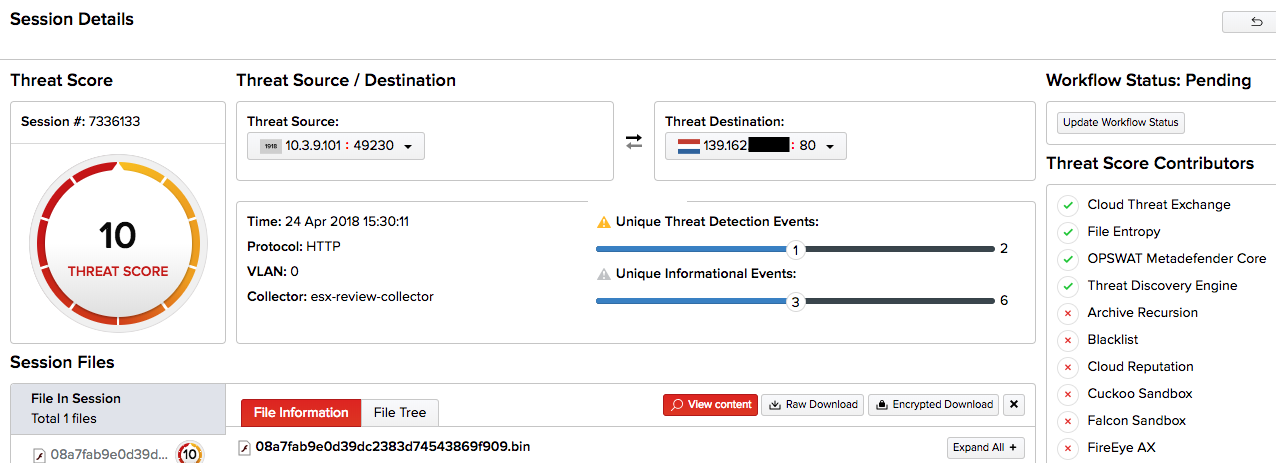
InQuest features threat scoring based on our own internal engine, augmented by Active Integrations: pluggable components which provide threat data that is weighted and then factored into our own assessment:
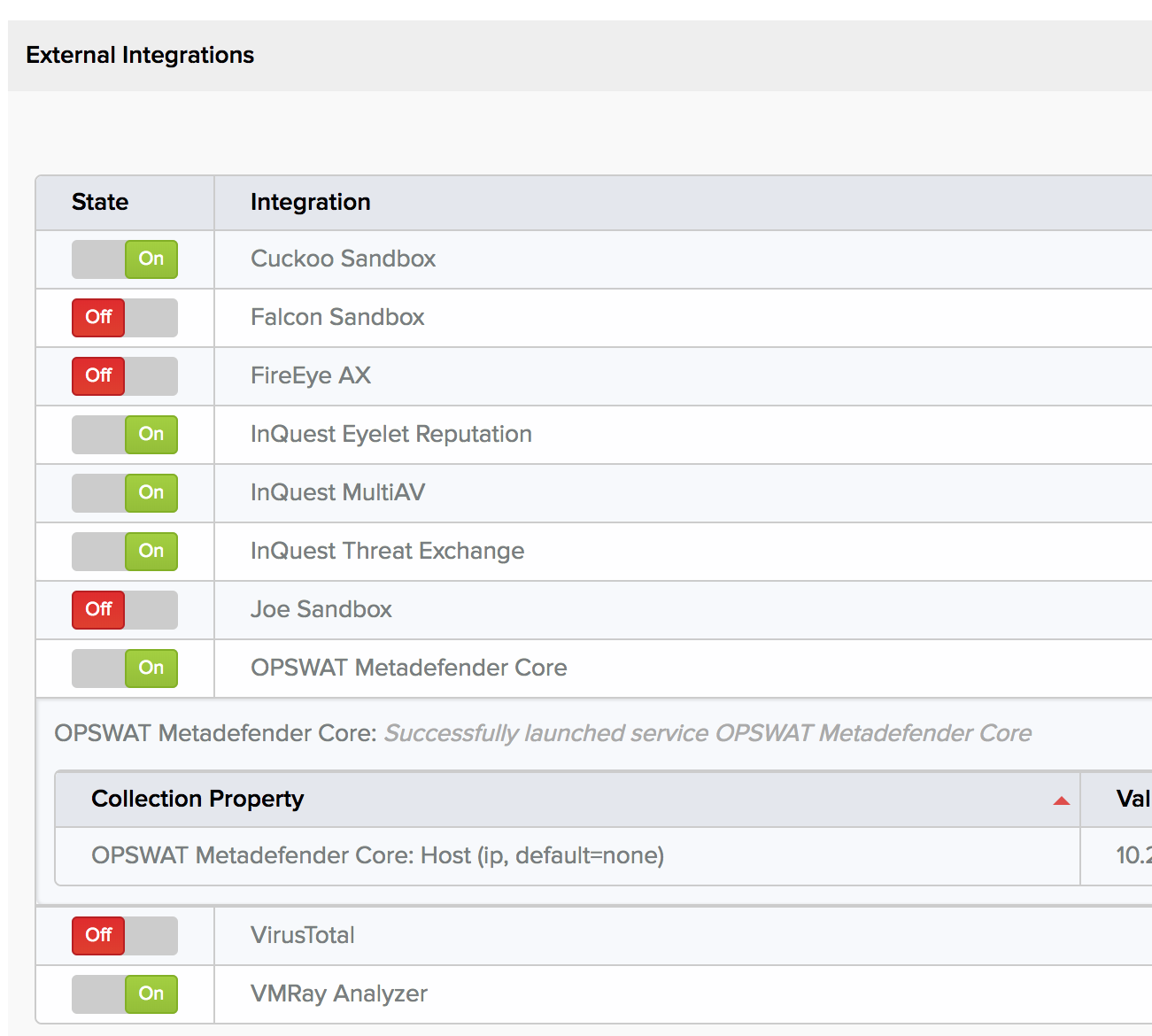
In other words, we use our “everything and the kitchen sink” approach to harvest and filter information to the point that an analyst can determine at a glance the reasoning behind a threat score, and therefore trust it. With both OPSWAT Metadefender and our other MultiAV Active Integrations, we interally evaluate and weigh results from individual AV products to give a more reliable “metascore.” For instance, a best-of-breed AV product with sophisticated analysis engines and frequently updated signatures will provide more reliable insight, and thus more valuable threat intelligence than a less mature product. By factoring those into our threat score, we can put everything under a single pane of glass, to give the analyst a solid basis for evaluation.
About OPSWAT
Founded in 2002 and based out of San Francisco, OPSWAT provides solutions to secure IT infrastructure to over 100 million endpoints around the world. Find out more about OPSWAT’s partnership with InQuest here.