On February 1st, Adobe published bulletin APSA18-01 for CVE-2018-4878 describing a use-after-free (UAF) vulnerability affecting Flash version 28.0.0.137 and earlier. As of February 6th, Adobe has patched the issue in version 28.0.0.161, see: APSB18-03. This post provides an overview of the vulnerability, a walk-through of the exploit seen in the wild, and covers several detection mechanisms. You can also follow the conversation via our Twitter moment.
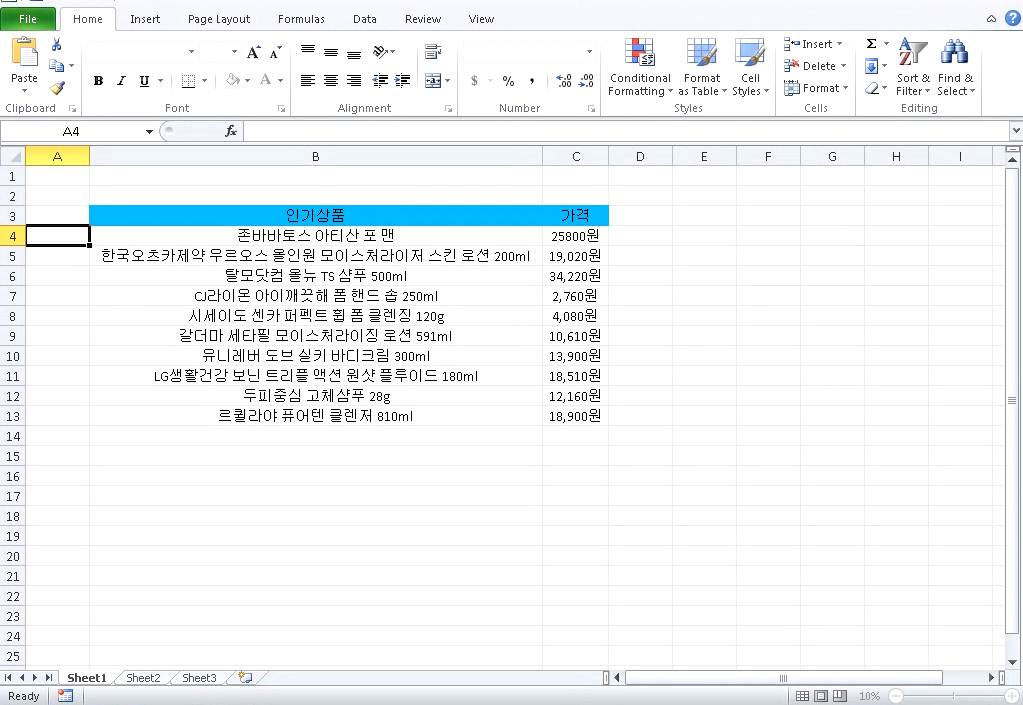
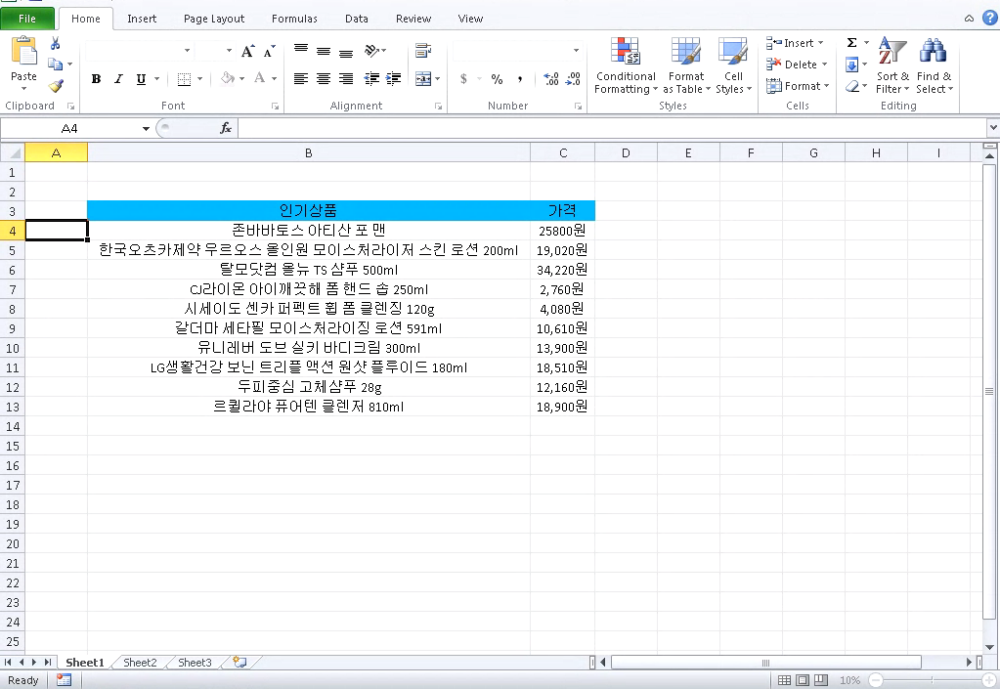
Screenshot of SWF 0day within Microsoft Office malware carrier document.Adobe Flash is on its final years as Adobe is scheduled to kill Flash in 2020. Major browsers such as Chrome, Microsoft Edge, and Safari have buried the functionality over the past year or so. There’s no denying that Flash has played a major role in the evolution of the web, arguably paving the way to HTML5. It was certainly nudged closer to the grave when Apple overtly decided against supporting the popular platform with the launch of the iPhone a decade ago.
From a consumer security perspective, this trend is generally a positive one; in 2015, there were 316 published Flash Player bugs (you heard that right, 6 bugs a week). The combination of a massive attack surface, ability to programatically manipulate memory, and mixed media access represents a dream come true for a potential attacker. While attackers quickly lose the ability to lean on Flash in the browser, the platform can still get them results through a medium such as Microsoft Office. On 1/31 the KrCERT/CC (South Korea Computer Emergency Response Team) released a notice regarding an Adobe Flash 0day exploit they observed in-the-wild, it was assigned CVE-2018-4878 and targets a UAF vulnerability in the TVSDK Platform. The exploit is delivered to targets in the following chain:
- Document based carrier. Both XLSX and DOC carriers have been observed in the wild.
- The carrier embeds Adobe Flash (SWF) content.
- Upon execution, the first-stage SWF exploit gathers system information and communicates with a compromised pivot server.
- A second-stage Adobe Flash payload is retrieved, decrypted, and executed. This second-stage payload contains the exploit for a use-after-free vulnerability in Adobe Flash MediaPlayer DRM management.
- The final payload, a ROKRAT Windows PE file is downloaded and executed.
Sparing transmission of the exploit to a second-stage is common sense from an OPSEC (operational security) perspective. By delaying the delivery of the 0day exploit, the attackers are limiting the exposure of this valuable capability. As such, the second-stage sample has not been widely reported on or analyzed. We’ve made all stages of the exploit chain available, along with ActionScript decompilation available on GitHub.com/InQuest.
Let’s walk through the exploit chain starting from the XLSX carrier 14c58e3894258c54e12d52d0fba0aafa258222ce9223a1fdc8a946fd169d8a12. Decompress the XLSX file and note /xl/activeX/activeX1.bin, at offset 0x18 (24) you’ll recognize Adobe Flash magic. Let’s carve it out:
$ xxd activeX1.bin | head
00000000: 6edb 7cd2 6dae cf11 96b8 4445 5354 0000 n.|.m.....DEST..
00000010: 6655 6655 97c8 0100 4657 5320 97c8 0100 fUfU....FWS ....
00000020: 7800 04e2 0000 0ea6 0000 1801 0044 1119 x............D..
00000030: 0000 007f 13cb 0100 003c 7264 663a 5244 .........<rdf:RD
00000040: 4620 786d 6c6e 733a 7264 663d 2768 7474 F xmlns_rdf='htt
00000050: 703a 2f2f 7777 772e 7733 2e6f 7267 2f31 p://www.w3.org/1
00000060: 3939 392f 3032 2f32 322d 7264 662d 7379 999/02/22-rdf-sy
00000070: 6e74 6178 2d6e 7323 273e 3c72 6466 3a44 ntax-ns#'><rdf:D
00000080: 6573 6372 6970 7469 6f6e 2072 6466 3a61 escription rdf:a
00000090: 626f 7574 3d27 2720 786d 6c6e 733a 6463 bout='' xmlns:dc
000000a0: 3d27 6874 7470 3a2f 2f70 7572 6c2e 6f72 ='http://purl.or
000000b0: 672f 6463 2f65 6c65 6d65 6e74 732f 312e g/dc/elements/1.
000000c0: 3127 3e3c 6463 3a66 6f72 6d61 743e 6170 1'><dc:format>ap
000000d0: 706c 6963 6174 696f 6e2f 782d 7368 6f63 plication/x-shoc
$ dd if=activeX1.bin of=swf skip=24 bs=1 count=999999
$ file swf
swf: Macromedia Flash data, version 32
Through a combination of swfdump and FFDec we can both ascertain the entry point and decompile the embedded ActionScript.
$ swfdump swf | egrep "FRAMELABEL|DOABC"
[02b] 8 FRAMELABEL "loadswf"
[052] 2788 DOABC "loadswf", lazy load
[052] 2686 DOABC "mx/utils/StringUtil", lazy load
[052] 264 DOABC "mx/core/IFlexAsset", lazy load
[052] 553 DOABC "mx/core/ByteArrayAsset", lazy load
[052] 355 DOABC "loadswf_SWFBClass", lazy load
[052] 339 DOABC "loadswf_MyURL", lazy load
[052] 206 DOABC "mx/core/mx_internal", lazy load
Stepping through the major portions of this first-stage payload:
- Entrypoint @loadswf
- Request to a compromised South Korean server to retrieve and decrypt the second-stage payload.
- XOR decoder
- Transfer control to second-stage
Stepping through the major portions of the second-stage payload (0day):
One variable that isn’t immediately apparent in the decompiled ActionScript is the URL which the second-stage SWF payload (0day) is retrieved from. We got lucky with a little Linux command line brute force extraction combined with domain knowledge of common URLs to filter:
$ grep -aEor 'https?://[A-Za-z0-9./]+' 14c58e3894258c54e12d52d0fba0aafa258222ce9223a1fdc8a946fd169d8a12/ | cut -d':' -f2- | sort | uniq | grep -Ev "adobe.com|w3.org|openxmlformats.org|microsoft.com" | sed "s/http:/hxxp:/"
hxxp://purl.org/dc/dcmitype/
hxxp://purl.org/dc/elements/1.1
hxxp://purl.org/dc/elements/1.1/
hxxp://purl.org/dc/terms/
hxxp://www.dylboiler.co.kr/admincenter/files/boad/4/manager.php
The last URL in that least clearly stands out. If heavily obfuscated, dynamic analysis would be the preferred extraction path.
Detection
We’ve made a number of relevant YARA signatures available on GitHub.com/InQuest for detecting the various components of this threat. Ordered from most general to most specific:
- Microsoft_Office_Document_with_Embedded_Flash_File.rule
- Adobe_Flash_DRM_Use_After_Free.rule
- CVE_2018_4878_0day_ITW.rule
While not explicitly indicative of malicious content, it’s prudent for a threat hunter to explore documents discovered in transit that embed Adobe Flash via the first rule. The second looks for specific triggers suspected in the decompiled ActionScript, efficacy of this signature is dependent on processing the captured SWF file through an engine such as FFDec. Generically, the $varc_1 string from this rule looks for the requisite components to trigger the UAF vulnerability within the bounds of a single function. The final signature above is mostly sourced from posts in the public domain (see references), we threw a tweak on it to avoid false positives. This signature, while exploit specific and more easily evadable, applies to the existing threats observed in the wild thus far.
IOCs
- 14c58e3894258c54e12d52d0fba0aafa258222ce9223a1fdc8a946fd169d8a12 Carrier: Microsoft Excel 2007+
- 3b1395f620e428c5f68c6497a2338da0c4f749feb64e8f12e4c5b1288cc57a1c Carrier: Composite Document File V2 Document
- 88d7aa1612756e2e70e4972d3f6a80517515f5274b38d4601357f954e207f294 Stage-1: Macromedia Flash data, version 32
- fec71b8479f3a416fa58580ae76a8c731c2294c24663c601a1267e0e5c2678a0 Stage-1: Macromedia Flash data, version 32
- 1a3269253784f76e3480e4b3de312dfee878f99045ccfd2231acb5ba57d8ed0d Stage-2: (0day) Macromedia Flash data (compressed), version 32
- e1546323dc746ed2f7a5c973dcecc79b014b68bdd8a6230239283b4f775f4bbd Payload: (ROKRAT) PE32 executable (GUI) Intel 80386, for MS Windows
- hxxp://www.dylboiler.co.kr/admincenter/files/boad/4/manager.php
- hxxp://1588-2040.co.kr/design/m/images/image/image.php
- hxxp://www.1588-2040.co.kr/conf/product_old.jpg
- hxxp://www.korea-tax.info/main/local.php
References (chronological)
- Twitter moment
- https://www.krcert.or.kr/data/secNoticeView.do?bulletin_writing_sequence=26998
- https://helpx.adobe.com/security/products/flash-player/apsa18-01.html
- http://blog.talosintelligence.com/2018/02/group-123-goes-wild.html
- https://www.fireeye.com/blog/threat-research/2018/02/attacks-leveraging-adobe-zero-day.html
- https://otx.alienvault.com/pulse/5a7437b59de8422ad47fc161
- http://blog.alyac.co.kr/1521
- https://blog.malwarebytes.com/cybercrime/2018/02/new-flash-player-zero-day-comes-inside-office-document/
- https://www.flashpoint-intel.com/blog/targeted-attacks-south-korean-entities/
- http://blog.morphisec.com/adobe-flash-zero-day-prevented-by-morphisec-cve-2018-4878
- https://helpx.adobe.com/security/products/flash-player/apsb18-03.html
- https://blog.morphisec.com/cve-2018-4878-an-analysis-of-the-flash-player-hack
- https://www.mdsec.co.uk/2018/02/adobe-flash-exploitation-then-and-now-from-cve-2015-5119-to-cve-2018-4878/
- https://github.com/mdsecactivebreach/CVE-2018-4878
Free On-Demand Webinar: Think Before You Click
Whether sent as an email attachment, sitting in your cloud or traversing the Web, file-borne threats have become a proven favorite for delivering malware and phishing campaigns. View our webinar on-demand and get firsthand tips about how to safeguard your cybersecurity stack with File Detection and Response (FDR) and stop file-borne threats in their tracks.